Update 16/04/2014: SAP have now released KnowledgeBase Article 2004805 – Heartbleed (CVE-2014-0160) OpenSSL Vulnerability – Product related status and recommendations (SAP Service Marketplace ID Required) which lists all available information on the vulnerability of SAP products to Heartbleed.
Heartbleed is a major security vulnerability that has been widely reported in the media in recent days.
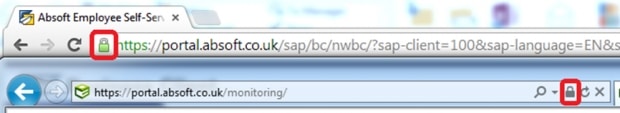
Heartbleed allows an attacker to read the memory of servers running certain releases of the openSSL library. This library is widely used for SSL (Secure Sockets Layer) or TLS (Transport Layer Security) including, in some cases, the secure padlock icon that appears on secure webpages.
Heartbleed allows memory of the server to be read by an attacker. This allows the security certificate to be comprised.
Fixing Heartbleed
The latest openSSL release 1.0.1g has been fixed so it is no longer vulnerable to Heartbleed. Any affected systems should be patched to this level.
If you have used a certificate with an affected openSSL version, that certificate could be compromised and should be revoked and renewed after openSSL is patched. You can contact the company you bought the security certificates from (Certificate Authority) to arrange this.
Is SAP Software Affected by Heartbleed?
At the time of writing, SAP have not made official announcements on how Heartbleed affects most of their products. The information contained in this blog is not from SAP and the security of your system should be verified by an SAP Security Consultant in all cases.
SAP generally implements SSL through the SAPCRYPTOLIB library which is different from openSSL. This means that, in general, SAP products should be secure. There are some key exceptions where Heartbleed could affect SAP. If any third party software is used in conjunction with your SAP software it could introduce a dependency on openSSL. It is important to rule out use of an affected openSSL version across your entire landscape.
Affected openSSL Versions
This list of affected openSSL versions states that versions 1.01 to 1.01f are vulnerable to Heartbleed. 1.0.1g is the fixed release, and the 1.0.0 and 0.9.8 branches are not vulnerable.
Generally most commercial software uses an older version such as 0.9.8 that is not affected. This significantly reduces the impact of the bug.
Linux Servers
If you run any part of your SAP landscape on Linux servers, you can check your Linux servers by checking the version of the openSSL packages. For Redhat and SuSE, you can use the command ‘rpm –qa | grep openssl’ as shown:
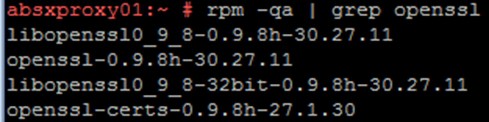
The version of the openssl package is key – in this case it is 0.9.8h which is not affected by Heartbleed so no further action is required.
Web Access to SAP
A key area where Heartbleed could affect SAP is with any web access to your SAP systems. If you are accessing SAP with a web browser, there is a possibility that some software using a vulnerable version of openSSL is present.
Typical SAP Systems are generally not affected directly as they use SAPCRYPTOLIB rather than openSSL. However, third party software such as reverse proxies or load balancing software could use openSSL. This software handles the outside connections to web services hosted by a SAP System.
SAP Web Dispatcher is SAP’s own reverse proxy and load balancing system that does not appear to be affected by Heartbleed.
Apache is a commonly used reverse proxy server for managing web access to SAP. If you use apache, you should check the openSSL library that is in use with the steps above.
You can check any web service that is open to the public internet with this tool to get an indication on whether the Heartbleed vulnerability could be present.
SAP BW Accelerator
SAP have published SAP KnowledgeBase Article 2004367 (SAP Service Marketplace ID required) stating that despite coming with an Apache webserver, SAP BW Accelerator is not vulnerable to Heartbleed because the Apache webserver is not started.
SAP HANA Cloud Platform
SAP have published a blog post stating that their SAP HANA Cloud Platform is not vulnerable to Heartbleed.
Amazon AWS Cloud
If you run any SAP services in the Amazon AWS Cloud, especially with their Elastic Load Balancing, they were previously vulnerable to Heartbleed but have now resolved it. They advise changing any SSL certificates that were in use whilst the vulnerability was present.
SAP BusinessObjects
SAP have released KnowledgeBase Article 2003582 – How does The Heartbleed Bug (OpenSSL vulnerability) affects SAP BusinessObjects Xi3.1 and Business Intelligence products 4/4.1 (SAP Service Marketplace ID required). This states that BusinessObjects is generally not affected by HeartBleed.
Other Software Using the Same Certificate
The nature of Heartbleed means that if a particular certificate is in use on any system that is vulnerable, then that certificate could have been compromised in the past. If any certificates you use in your SAP landscape, such as any maintained in transaction STRUST, are also in use elsewhere then it’s important to check all affected systems.
Summary
Heartbleed has the potential to affect SAP systems depending on which third-party software components are present. The steps above give some tips on checking how vulnerable you are, but assumptions cannot be made that the Heartbleed vulnerability is not present in your landscape. Contacting an SAP Security Consultant to ensure the security of your systems is recommended in all cases.
Disclaimer
The information contained in this blog is for general information purposes only. The information is provided by Absoft and whilst we endeavour to keep it up-to-date and correct, we make no representations or warranties of any kind, express or implied, about the completeness, accuracy, reliability, suitability or availability with respect to the blog. Any reliance you place on such information is therefore strictly at your own risk.
In no event will we be liable for any loss or damage including without limitation, indirect or consequential loss or damage, or any loss or damage whatsoever arising from loss of data or profits arising out of, or in connection with, the use of this blog.