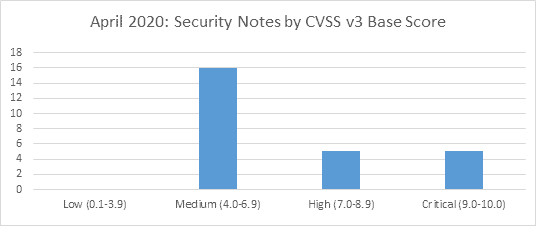
SAP’s security patch day for April 2020 has seen the release of 26 OSS SAP security notes. 16 OSS notes have been classified as medium, 5 OSS notes have been classified as high and 5 as critical, based on CVSS v3.0 Rating.
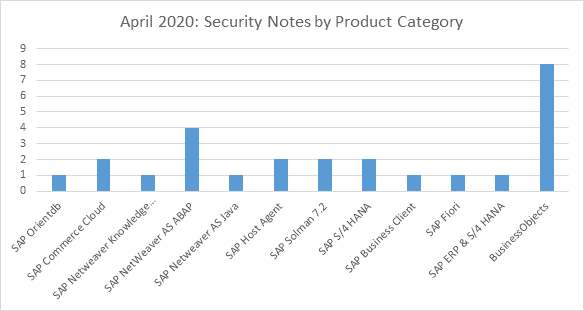
A single security OSS note this month has been found to the SAP Orientdb, and another one for the SAP Netweaver Knowledge Management. In addition to that, one security vulnerability has been found for the following products: SAP Netweaver AS Java, SAP Business Client, SAP Fiori, SAP ERP & S/4 HANA. Also, two security vulnerability notes have been found for the: SAP Commerce Cloud, SAP Host Agent, Solution Manager and S/4 HANA. Lastly, four security vulnerabilities have been found for the SAP Netweaver AS ABAP, and eight for the Business Objects.
Vulnerabilities: April 2020 Highlights
[CVE-2020-6230] Code Injection vulnerability in SAP OrientDB 3.0 (SAP Note 2900118)
SAP OrientDB 3.0 allows an authenticated attacker with script execute/write permissions to inject code that can be executed by the application and lead to an elevation of privileges. An attacker could thereby control the behaviour of the application. The attack can only be executed by authenticated users with script execute privilege. This may impact existing users with Javascript functions defined in OrientDB, expecting access to certain Java classes. It is recommended from the OSS note 2900118 to upgrade to at least the version OrientDB 3.0.29.
[CVE-2020-6208] Remote Code Execution in SAP Business Objects Business Intelligence Platform (Crystal Reports) (SAP Note 2861301)
Crystal Reports Designer allows an attacker with basic authorization to inject code that can be executed by the application. The attacker could hence control the behaviour of the application. In order to overcome the vulnerability, it is suggested that patching to the latest SP level has to take place on the Business Objects platform.
Update 2 to Security Note 2808158: [CVE-2019-0330] OS Command Injection vulnerability in SAP Diagnostics Agent (SAP Note 2839864)
There was a vulnerability found which allows arbitrary code to be executed. The original correction did not cover all scenarios, so the OSS note 2839864 corrects these additional ones. The vulnerability was found in one of the core Solution Manager components, so this should be patches or the note applied as soon as possible.
[CVE-2020-6234] Privilege Escalation in SAP Host Agent (SAP Note 2902645)
An attacker with Host Agent admin privileges may use the SAP Host Agent’s Operation Framework to gain root privileges over the underlying operating system. The recommendation of the OSS note 2902645 is to upgrade SAP Host Agent to at least version 7.21 PL46.
[CVE-2020-6235] Missing authentication check in SAP Solution Manager (Diagnostics Agent ) (SAP Note 2906994)
The Diagnostics Agent does not perform the authentication check for the functionalities of the Collector Simulator. The fix enables user authentication in the Collector Simulator Servlet. The vulnerability at the OSS note 2906994 was found in one of the core Solution Manager components, and patching of the solution manager is suggested to overcome the vulnerability.
[CVE-2020-6219] Deserialization of Untrusted Data in SAP Business Objects Business Intelligence Platform (CrystalReports WebForm Viewer) (SAP Note 2863731)
Crystal reports web form viewer allows an attacker with basic authorization to perform deserialization attack in the application, which may lead to code execution upon it. The attack occurs when untrusted data is used to manipulate the logic of the application. An attacker modifies certain parameters in the Viewer to perform the attack. In order to overcome the vulnerability, it is suggested that patching to the latest SP level has to take place on the Business Objects platform.
[CVE-2020-6225] Directory Traversal vulnerability in SAP NetWeaver (Knowledge Management) (SAP Note 2896682)
SAP NetWeaver Knowledge Management does not sufficiently validate path information provided by users, allowing an attacker to overwrite, delete, or corrupt arbitrary files on the remote server, leading to Path Traversal. In order to overcome the vulnerability, it is suggested to patch Knowledge Management component.
[CVE-2020-6237] Information Disclosure in SAP Business Objects Business Intelligence Platform (dswsbobje Web Application) (SAP Note 2898077)
Under certain conditions SAP Business Objects allows an attacker to access information which would otherwise be restricted. In order to overcome the vulnerability that it is described in the OSS note 2898077, it is suggested that patching to the latest SP level has to take place on the Business Objects platform.
[CVE-2020-6238] Missing XML Validation vulnerability in SAP Commerce (SAP Note 2904480)
SAP Commerce does not process XML input securely in certain REST XML APIs. This affects confidentiality and availability (partially) of SAP Commerce. The suggestion from the OSS note 2904480 is to patch SAP Commerce Cloud.
2902456 – [CVE-2020-6236] Privilege Escalation in SAP Landscape Management (SAP Adaptive Extensions) (SAP Note 2902456)
An attacker with admin_group privileges could change ownership and permissions of arbitrary files remotely. This results in the possibility to execute these files as root user from a non-root context. In combination with other typically available remote functions on SAP systems, one may change ownership and permissions to execute arbitrary commands on the target system as root user. The recommendation is to upgrade SAP Host Agent to at least version 7.21 PL46.
About this review
On the second Tuesday of each month, SAP release security updates to their software products. At Absoft, we analyse all of the released security updates and produce this security review, including sending bespoke recommendations for each of our managed service customers.
There is more information on how we handle SAP security updates, including information on SAP’s process, the CVE process and the CVSS base scores in our earlier article on addressing security vulnerabilities in SAP software.