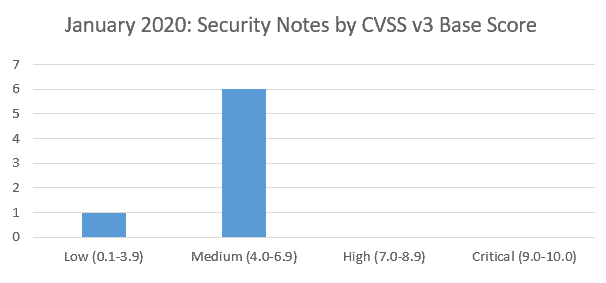
SAP’s security patch day for January 2020 has seen the release of 7 SAP security notes. There is good news this month that there are no critical or highly scored vulnerabilities requiring a fix based on CVSS v3.0 Rating.
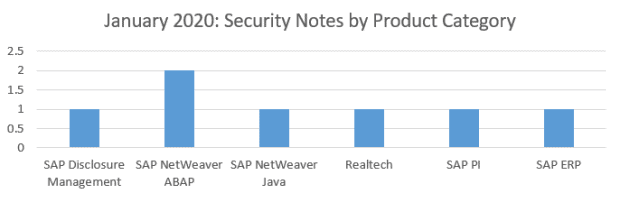
3 of this month’s vulnerabilities affect the NetWeaver platform – having a wider impact across many customers. The other 4 are specific to individual products:
Vulnerabilities: January 2020 Highlights
Missing Authorization Check in Automated Note Search Tool (SAP Note 2863397)
The Automated Note Search Tool (ANST) could potentially reveal sensitive information because an authorisation object check is missing from some of the more advanced functionality. This is marked as only medium criticality as the user has to already be logged on and have privileged access to begin with. The SAP note or latest support package stack should be applied to correct this.
Denial of service (DOS) in SAP NetWeaver Internet Communication Manager (SAP Note 2848498)
A vulnerability is found on the Java part of the SAP NetWeaver kernel which affects the ICM – SAP’s web server. A buffer overflow is possible which could cause it to become unavailable and lead to a DoS attack. The solution to correct this vulnerability is to apply the latest Kernel from SAP.
About this review
On the second Tuesday of each month, SAP release security updates to their software products. At Absoft, we analyse all of the released security updates and produce this security review, including sending bespoke recommendations for each of our managed service customers.
There is more information on how we handle SAP security updates, including information on SAP’s process, the CVE process and the CVSS base scores in our earlier article on addressing security vulnerabilities in SAP software.