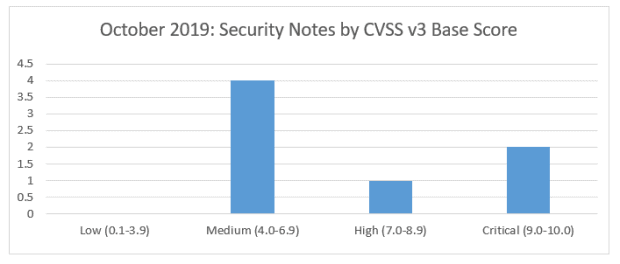
SAP’s security patch day for October 2019 has seen the release of 7 SAP security notes with 1 High and 2 Critical CVSS v3.0 Rating.
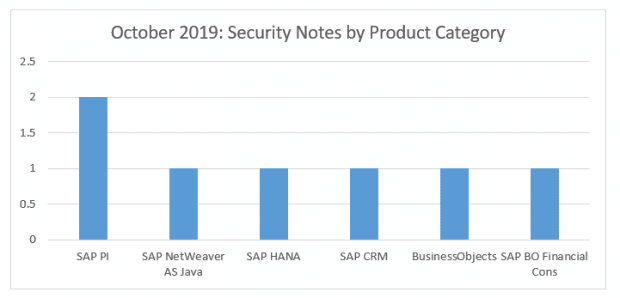
Two of the vulnerabilities relate to authorization check exploits for the SAP PI, but the B2B Add On only. One vulnerability relates to SAP HANA for Binary planning, where the SAP SQL Anywhere, SAP IQ and SAP Dynamic Tiering are used. One security note is applicable for any systems implementing SAP Landscape Management (LVM) – the attack can only be performed under very specific, uncommon conditions, but could result in the exposure of critical information. There are two notes related to Business Objects, one for XSS in Business Intelligence, the other being specific to the BO Financial Consolidation component only. An XSS vulnerability has also been identified for customers utilizing Email management in SAP CRM.
Vulnerabilities: October 2019 Highlights
[CVE-2019-0380] – Information Disclosure vulnerability in SAP Landscape Management Enterprise (Note 2828682)
LVM (LaMa) connectivity could be manipulated into returning additional information which would otherwise be restricted. The solution includes implementing the updated patch for the component in additional to a number of manual steps detailed in the note.
[CVE-2019-0379] – Missing Authentication Check in AS2 Adapter of B2B Add-On for SAP NetWeaver Process Integration (Note 2826015)
Affecting only the B2B Add On for PI, this vulnerability allows access to administrative or privileged functions because authorization checks for some functionalities do not require user identity to be provided. The solution requires applying the latest support package as detailed in the note, but an immediate risk mitigation can be performed by altering system properties as detailed in the note.
[CVE-2019-0381] – Binary Planting vulnerability in SAP SQL Anywhere, SAP IQ and SAP Dynamic Tiering (Note 2792430)
Systems utilising SAP’s SQL Anywhere, IQ or Dynamic Tiering as part of a SAP HANA implementation could have the file search algorithm manipulated into disclosing directories outside the path specified by a user who already has access to the system. Implementation of the latest support packages as detailed in the note is required to resolve the issue.
About this review
On the second Tuesday of each month, SAP release security updates to their software products. At Absoft, we analyse all of the released security updates and produce this security review, including sending bespoke recommendations for each of our managed service customers.
There is more information on how we handle SAP security updates, including information on SAP’s process, the CVE process and the CVSS base scores in our earlier article on addressing security vulnerabilities in SAP software.